Hardware tokens for Native OTP Authentication with NetScaler
Citrix NetScaler One Time Password (OTP) feature is introduced with NetScaler 12.0 FR1. This feature offers OTP authentication capabilities without having to use a third party server. In addition, it consolidates configuration within the NetScaler, thus offering great control to administrators.
This guide describes the user interface flow for enabling Token2 programmable tokens with the Native OTP capability already activated. Native OTP configuration procedures are described here.
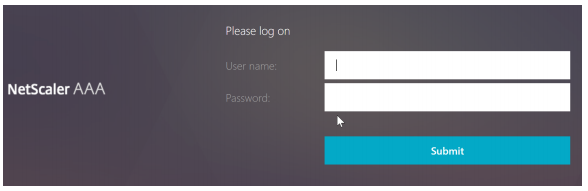
Navigating to ManageOTP URL e.g., https://otpauth.server.com/manageotp (alternatively, you can use https://alt.server.com if you have configured host-based management page), we will be presented with initial logon page that only requires ldap logon credential:
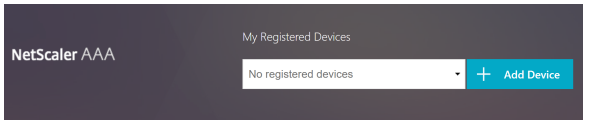
After login with a valid credential, we will see the manage device page as follow:
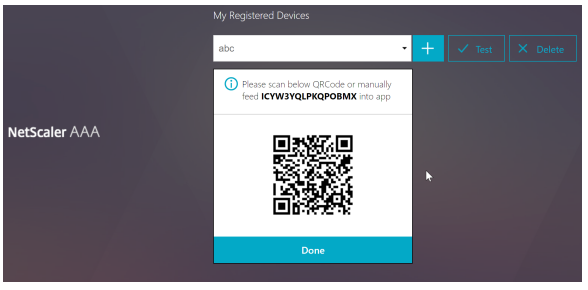
After click ‘+’, type in the device name, click ‘go’, and click ‘done’, we will see a QR code generated. This indicates the device has been registered:
The next step is provisioning (burning) the hardware token:
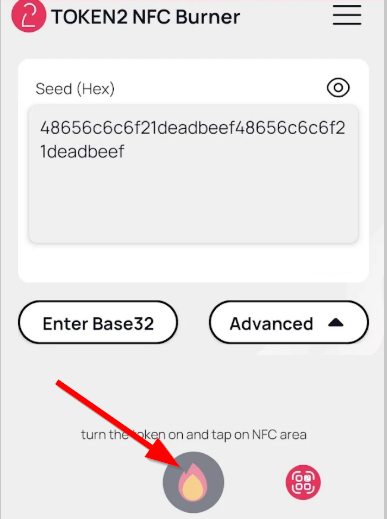
- Launch the NFC burner app on your Android device and hit the "QR" button
- Point the camera to the QR code shown on the account page. Upon a successful QR scan, the camera window should disappear
- Turn on the token and touch it with your phone (make sure it is overlapped by the NFC antenna) and click "Connect" on the app
- Upon successful connection, click the "Burn seed" button (the button will become active only if NFC link is established).
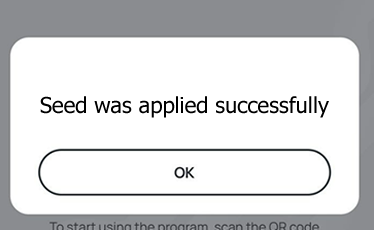
- A message box similar to the one below will be shown upon successful completion
Follow the steps below to perform setting the seed for your token using Windows App.
1. Launch the exe file, then select the NFC device from the drop-down list and click on "Connect". You should see a message box notifying about a successful operation.
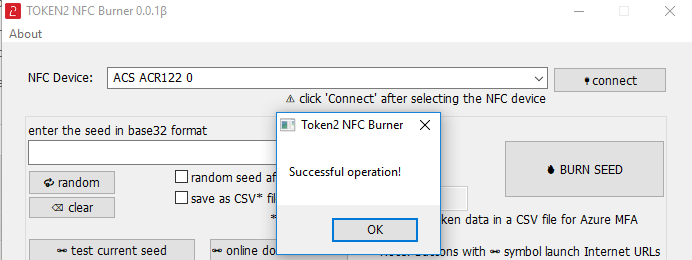
2. Enter or paste the seed in base32 format, or use one of the QR scanning methods to populate this field
3. Place the token onto the NFC module and wait for its serial number to appear.
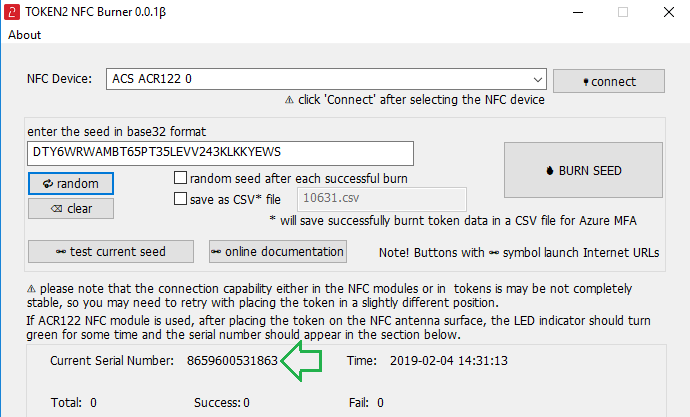
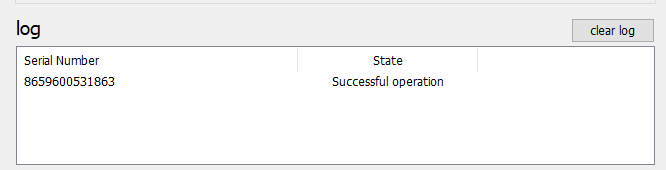
4. Click on "Burn seed" button. A log entry with the serial number and "Successful operation" text will be logged in the log window.
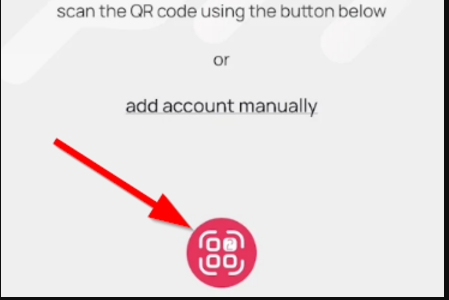
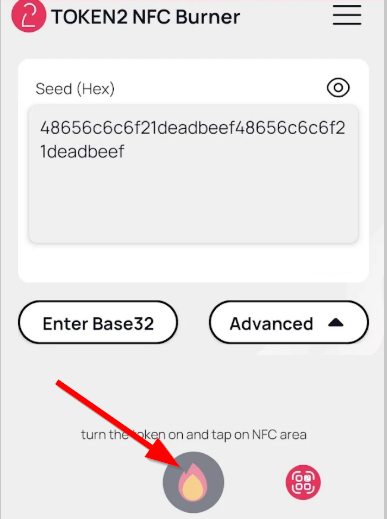
- Launch the NFC burner app on your iPhone device and hit the "scan QR" button
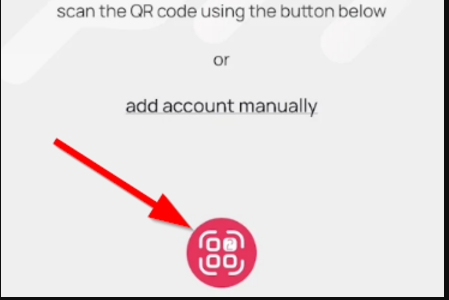
- Point the camera to the QR code shown on the account page. Upon a successful QR scan, the camera window should disappear and the seed field will be populated with the hex value of the seed. Touch the Burn button to continue.
- When an NFC prompt similar to the one below is shown, turn on the token and touch the top of your iPhone with the token.
- A message box similar to the one below will be shown upon successful completion
An OTP generated by your token can be entered to test the newly registered device.
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!