TOTPRadius - RADIUS Dynamic attribute response based on AD Group membership
This can be configured in Settings → RADIUS Service configuration:
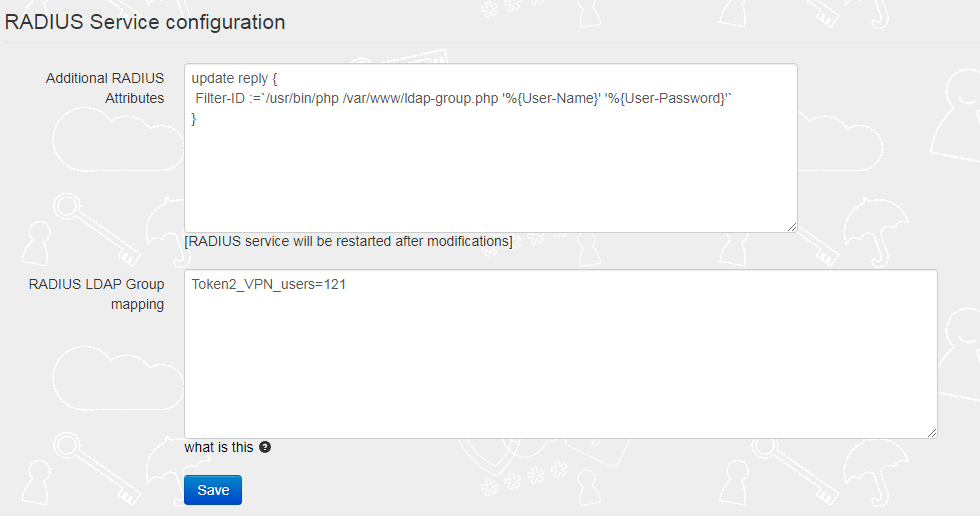
The 'Additional RADIUS Attributes' field should contain the reference to the ldap-group script as shown on the example below:
update reply { Filter-ID :=`/usr/bin/php /var/www/ldap-group.php '%{User-Name}' '%{User-Password}'` }
Important: The group names used for this parameter should not contain "=" sign.
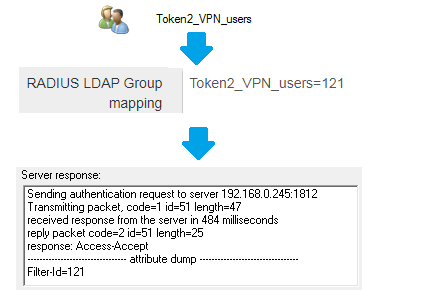
The 'RADIUS LDAP Group mapping' field should contain a mapping rule, which allows members of the specified AD group to have Tunnel-Private-Group-ID attribute equal to some value.
For the example above, if a user belongs to an AD Group named 'Token2_VPN_users', the Filter-ID will be included in the Radius reply as below:
About
Installation and configuration
- Installation and initial configuration
- Network configuration
- Migrating from older versions
- LDAP Configuration
- Azure AD Configuration
- Self-service enrollment portal
- Web and LDAPS Certificates
- Syslog configuration
- Single-factor authentication exceptions
- Slave appliance mode
- Dynamic RADIUS Attributes
Integration guides
Blog
18-07-2025
Windows 11 Update KB5062553 Breaks FIDO2 Security Key Management
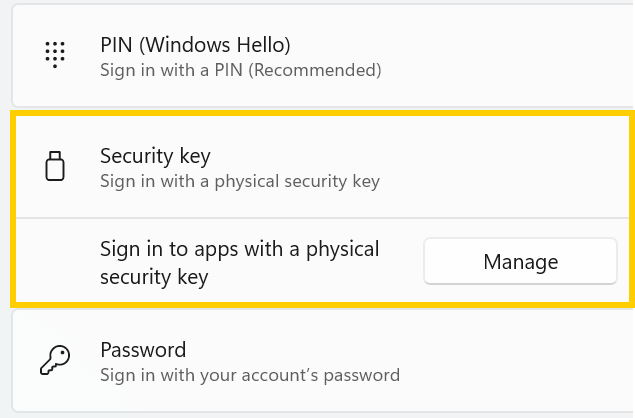 A recent Windows 11 update — KB5062553 — appears to have introduced a critical issue affecting FIDO2 security key management.
A recent Windows 11 update — KB5062553 — appears to have introduced a critical issue affecting FIDO2 security key management.
27-06-2025
Token2 PIN+ Bio3 Now Available
 Now Available: Token2 Bio3 – The First Biometric FIDO2 Key with Dual USB-A/USB-C Interface and iOS Fingerprint Management
Now Available: Token2 Bio3 – The First Biometric FIDO2 Key with Dual USB-A/USB-C Interface and iOS Fingerprint Management
06-06-2025
Token2 PIN+ Now Compatible with ID-Austria
 Only a handful of countries have adopted FIDO2 for secure authentication in public services. Switzerland’s AGOV platform was one of the early adopters, and it officially supports Token2 FIDO2 keys. We’re pleased to announce that Austria is now following suit.
Only a handful of countries have adopted FIDO2 for secure authentication in public services. Switzerland’s AGOV platform was one of the early adopters, and it officially supports Token2 FIDO2 keys. We’re pleased to announce that Austria is now following suit.
